Ouf offering includes:
- Vulnerability Management
- SIEM (Security Information and Event Management)
- EDR (Endpoint Detection and Response)
- XDR (Extended Detection and Response)

Advantages of the CyberVerse service – Deployment
- Faster protection against threats – instead of wasting time on manual configuration and system adjustment, you receive a ready-made, optimized solution from us that immediately begins protecting your IT infrastructure.
- Effortless security – there is no need to involve your team in the deployment process, or, in the assisted variant, we help you navigate the demanding parts of the process.
- Full utilization of the purchased solution – professional deployment means the platform is configured according to best practices, ensuring you gain maximum benefit and security.
- Fewer errors and better effectiveness – self-implementation can lead to security gaps. As EXATEL, we ensure the correctness of the deployed solution.
- Time and cost savings – reduction of expenditures on internal training and experimental configurations within the organization. Instead, you receive a platform tailored to your needs.
- Expert support at every stage – as part of the deployment, you gain access to specialists who will not only launch the platform but also train your team upon request.
- Scalability – the platform is deployed in a way that is adapted to organizational growth.
- Possibility of testing in the form of a Proof of Concept.
- Integration capabilities with client systems (e.g., SIEM, AD (Active Directory), ITSM (Information Technology Service Management), etc.).
Advantages of the CyberVerse service – Management
- Time savings – as EXATEL, we take over all responsibilities related to platform administration, allowing you to better focus on operational activities.
- Always up-to-date and optimal configuration – every month, we optimize the platform according to manufacturer recommendations and current security standards, ensuring full use of the platform’s capabilities.
- Reduced risk of security incidents – we provide professional security policy management and configuration updates, minimizing the risk of administrative errors and reducing the attack surface.
- Easy solution scalability – the ability to adapt to your needs, from small companies to large enterprises, alongside changing requirements and needs.
- Constant access to specialists – as EXATEL, we provide access to experts specializing in the management and maintenance of cybersecurity platforms, so you don’t have to worry about staffing shortages. The service is delivered entirely by EXATEL’s in-house team.
- Reduction of team maintenance expenses.
Vulnerability Management:
A comprehensive solution for the proactive discovery, assessment, categorization, and remediation of security gaps. Utilizing advanced risk analysis and automated scanning, this service empowers security teams with enhanced vulnerability identification. As a result, it ensures IT environment stability and effectively reduces the risk of potential incidents.
Key Benefits:
- Full Vulnerability Visibility: Identification of security flaws across networks, operating systems, applications, and endpoints.
- Risk Prioritization: A dedicated risk score indicates the severity of each vulnerability, determining if it poses a real-time threat requiring immediate action.
- Continuous Monitoring: Automated, regular, and customizable environment scans that replace traditional, one-off security audits.
- Regulatory Compliance: Ready-to-use reports that support meeting audit and regulatory requirements.
- Time Savings and IT Efficiency: Automation of discovery and reporting processes, eliminating the need for manual analysis.
Target Audience:
- Organizations with Heightened Security Requirements: Companies in sectors such as public administration (including local government), energy, finance, law, manufacturing, or healthcare, where compliance (e.g., ISO 27001, GDPR) and continuous risk monitoring are critical.
- Large Organizations with Distributed IT Infrastructure: Entities operating remotely or using cloud/hybrid environments. The service enables centralized scanning of servers, workstations, network devices, and cloud systems from a single dashboard.
- Small and Medium-Sized Enterprises (SMEs): Companies without an extensive internal cybersecurity team that still require full visibility of system vulnerabilities and effective management tools.
What You Gain:
- Complete and up-to-date insight into gaps and threats across your entire IT infrastructure.
- A structured and transparent risk management process.
- Faster response times to emerging vulnerabilities.
- Reduced workload for IT and Security teams through automation and daily operational support.
- Consistent data for audits, ensuring compliance with industry standards and regulations.
Service Delivery Models (Vulnerability Management)
| License Resale | Platform Implementation | Managed Vulnerability Service |
|---|---|---|
| Selection and resale of licenses tailored to the number of assets, environment type, and organizational requirements. |
|
|
Why Vulnerability Management?
In complex IT environments, simple vulnerability scanning is no longer enough to effectively mitigate risk. Vulnerability Management organizes the entire process, allowing you to focus on discovering and eliminating gaps that truly impact your security posture. The solution provides full visibility into the vulnerability status of your entire IT infrastructure—from on-premise assets and cloud environments to network devices—enabling proactive risk management.
Technology partner:
SIEM (Security Information and Event Management)
SIEM is a platform that enables the centralized collection, normalization, and correlation of logs from IT systems, applications, network devices, and cloud environments. It provides a single, consistent location for security event analysis and the storage of data required for audits and regulatory compliance.
Key Benefits:
- Centralized Event Visibility: A single point of analysis for logs and events across the entire IT environment (infrastructure, apps, and cloud).
- Faster Threat Detection: Real-time event correlation and data analysis allow for earlier identification of potential incidents.
- Scalability: The architecture allows for flexible expansion of monitored data as the organization grows.
- Better Use of Security Data: SIEM data supports not only security processes but also operational analysis and auditing.
- Audit Readiness and Compliance: Unified log formats and advanced reporting simplify meeting requirements for standards such as ISO 27001, GDPR, and other local regulations.
- Foundation for SOC and Automation: SIEM serves as the base for 24/7 monitoring, SOC integration, and scenario-based response automation.
Target Audience:
- Medium and Large Enterprises: Organizations with extensive, distributed IT infrastructure and multiple log sources requiring central correlation.
- Regulated and High-Risk Organizations: Entities requiring advanced event analytics and high-level cybersecurity.
- Sectors: Finance, Energy, Large-scale Manufacturing, Retail, Healthcare, and Telecommunications.
Sectors: finance, energy, heavy industry, retail, healthcare, telecommunications.
Why SIEM:
Service delivery models:
| License Resale | SIEM Platform Implementation | Monitoring and Incident Response Service |
|---|---|---|
|
Selection and sale of SIEM platform licenses tailored to:
|
|
If you are interested in continuous security monitoring and incident response, explore our Security Operations Center (SOC) offering.
|
In modern IT environments, security event data is scattered across multiple systems. A lack of centralization and unified log formats hinders effective analysis, delays incident detection, and complicates reporting. A SIEM platform organizes security data and significantly increases operational efficiency.
Technology partner:
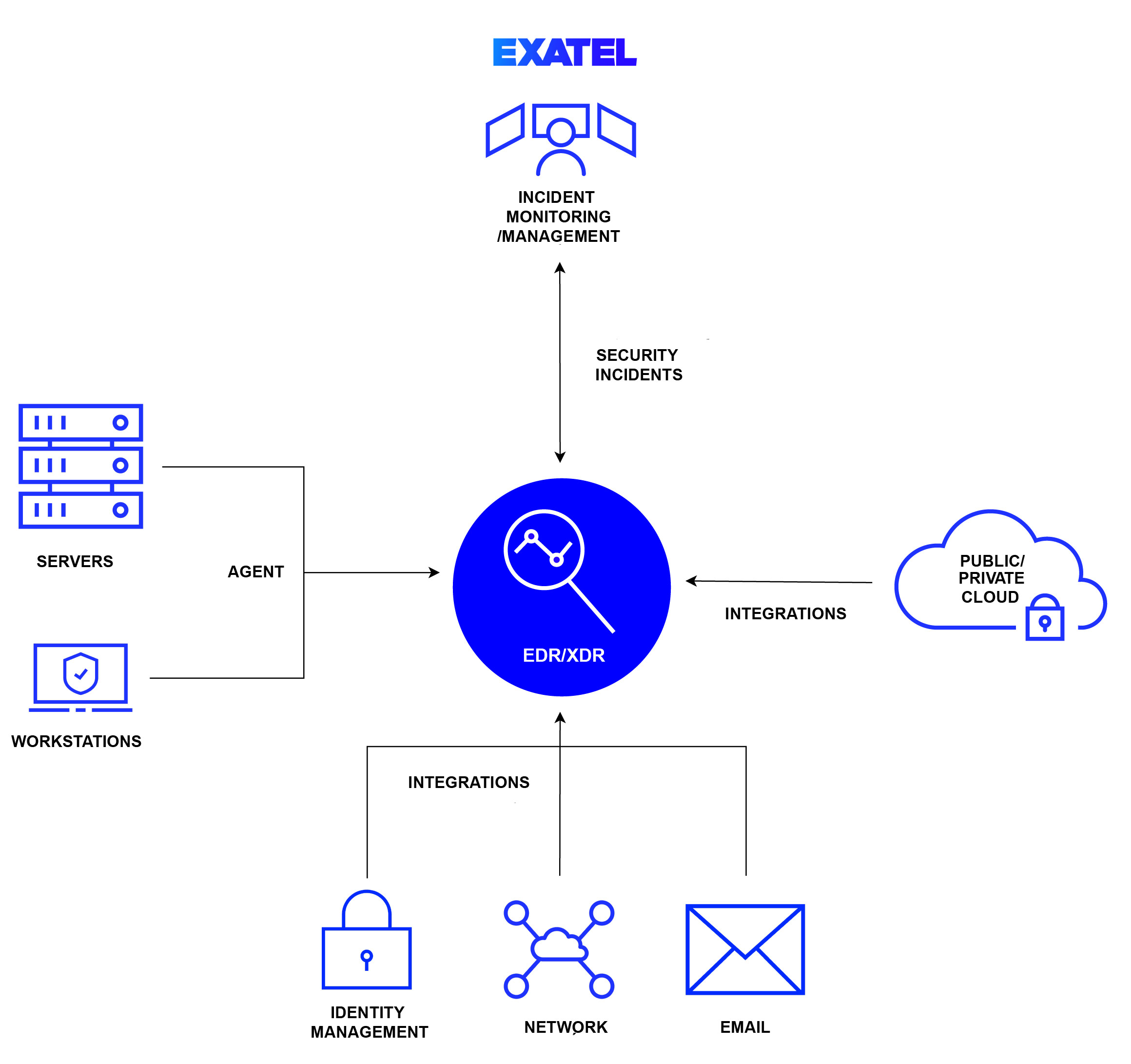
EDR/ XDR
- EDR (Endpoint Detection and Response)
is a solution that monitors and collects data from endpoints (computers, servers, mobile devices) to detect and respond to events. This enables the identification of abnormal activities, root cause analysis, and mitigation through automated incident responses, minimizing damage and risk. Thanks to EDR, analysts and system administrators can perform detailed analyses of security-related events. EDR is a real-time solution, meaning it is capable of detecting and responding to threats almost immediately after they appear. With this solution, organizations can significantly raise their security level and minimize risks associated with threats and attacks. EDR is also able to monitor both user behavior and the devices themselves.
- XDR (Extended Detection and Response)
is a more advanced version of EDR that extends monitoring and protection to other elements of the IT infrastructure, such as networks, servers, email, or cloud services. It provides greater visibility than EDR, ensuring a more holistic approach to threat detection across various layers of IT infrastructure. It enables data correlation from multiple sources (e.g., network, cloud, applications) and automates responses to complex attacks. As a result, the client receives more comprehensive protection.
EDR/XDR Deployment Models
| Activity | Custom Deployment | Full Deployment | Assisted Deployment |
|---|---|---|---|
| Agent installation on servers and workstations | Scope determined individually | Deployment of all endpoints provided by the client | Preparation of instructions for each OS type and assistance with initial installations per host type |
| Integration with custom systems | Individual valuation | No | No |
| Integration with standard systems | Optional | Yes | Delivery of instructions and assistance with the integration of the first system |
| Integration with client systems (e.g., SIEM, JIRA, etc.) | Optional | No | No |
| Creation of security policies | Determined during needs analysis | Configuration of all permission groups | Preparation of instructions and assistance in configuring 5 permission groups |
| Handover of post-deployment documentation | Optional | Optional | Only provided instructions |
| Functional and security tests | Optional | One week of testing in each mode: detect-detect, protect-detect, and protect-protect | No |
| IT Administrator training | Individual valuation | No | No |
Managed EDR/XDR
| Activity | Platform Support | Incident Monitoring | Full (Support + Monitoring) |
|---|---|---|---|
| Creating or changing security policy configurations (on request) | ✔ | ✖ | ✔ |
| Creating and changing exclusions for security policies (on request) | ✔ | ✖ | ✔ |
| Service request handling | ✔ | ✖ | ✔ |
| Contact with manufacturer service and coordination of requests | ✔ | ✖ | ✔ |
| Security incident monitoring | ✖ | ✔ | ✔ |
| False alarm detection | ✖ | ✔ | ✔ |
| Incident response (Isolation, process stopping, file analysis, rule updates) | ✖ | ✔ | ✔ |
| Regular agent updates on end stations | ✖ | ✔ | ✔ |
| Regular active management and optimization of security policies | ✖ | ✔ | ✔ |
| Monthly incident reporting | ✖ | ✔ | ✔ |
Technology partner: